Welcome to my blog!
I’ve been playing with the idea of starting a blog for a while, as there are already so many amazing networking & wireless blogs out there (see my blog-roll-ception on the home page) I wanted to ensure I could provide some useful content of my own.
I’m sure you’re well aware that not all devices are the same in the world of networking, and especially wireless networking. While I am not a Mac user, I am envious of some of the native capabilities in MacOS that provide some handy Wi-Fi tools, including some brilliant apps by Adrian Granados (check out AirTool). I also like the fact you can view detailed Wi-Fi info from the menu bar. This is handy when analysing client roaming behaviour and viewing the changes in signal strength and BSSID as a client associates to a new AP.
So that made me wonder if us Windows users could utilise something similar. I came across a handy Netsh command: ‘netsh wlan show interface’
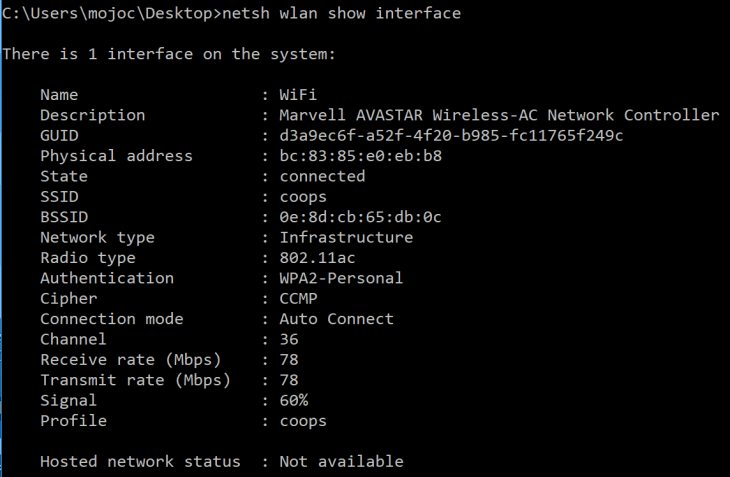
We see more information compared to the usual ‘ipconfig /all’; we can see BSSID, authentication method, radio type, cipher, channel, data rates and signal. Now, the latter I have noticed not to be accurate and it is dependent on the Wi-Fi chipset and driver (this is my Surface Pro 2017). If you want to see even more information you can run ‘netsh wlan show wlanreport’.
So I was happy to discover this command, but wanted more. There have been many scenarios where I’m testing roaming (in this instance verifying an 802.11r bug) walking around with a continuous ping, a multi-adapter packet capture, a WLC debug running… I want to easily refresh this ‘netsh’ command.
So here’s a little gift to you all, a bat file that refreshes the command at the hit of any key!
Download ‘netsh wlan.zip‘ (disclaimer: this file was free of viruses/malware when uploaded).
I hope you enjoyed my first post, feel free to leave a comment below and please follow as I will add more content!
EDIT: Update! I’ve purchased a 2015 MacBook Air and have been playing around with Adrian’s tools (Wi-Fi Explorer, AirTool, and Wi-Fi Check) as well as trying out some tools native to Linux such as nmap and sslcan for vulnerability analysis. Great fun!
